Today is International Coffee Day so what better day to take the Open Rights Group tag line of “Filters Are For Coffee Not The Internet” and investigate the capabilities of the Internet filtering at various coffee locations.
Costa Coffee / Cafe Nero – O2 Wifi
DNS Spoofing: Partial
MiTM SSL: No
Deep Packet Inspection: Yes
Destination IP Transit Interference: Yes
O2 WiFi requires two-factor registration via a phone number and SMS claiming that it is a legal requirement. This is easily traversed with a disposable PAYG phone (e.g. EE have a Nokia 106 for £4.99 – an excellent option for a burner phone). Once you’ve completed the two-factor check (the first being they record your MAC address) you can start browsing.
The first thing to notice is that unlike their mobile offering the WiFi has several layers of filtering, some DNS queries are intercepted to send you to a block page and even if you resolve the A record out-of-band Squid will intercept and block.
If you manually query a 3rd party DNS server for the record in question then it appears to return normally.
This level of blocking however is hit and miss with domains such as the thepiratebay.se suffering the worst interference but others that are blocked by the default mobile filters aren’t blocked on the WiFi.
Thankfully all the usual bypass methods (Tor, RoutingPacketsIsNotACrime.uk, SSH SOCKS5 tunnel and SSL) work flawlessly despite the use of Squid and DNS interference.
Interestingly O2 have chosen to force Google to not allow SSL searching (so they can inspect the content and block stuff) which also means anyone else in the coffee shop can spy on your browsing. DuckDuckGo.com does still offer SSL searching and isn’t blocked.
Breaking down an O2 Intercept
The packet capture for this attempt to hit http://reddit.com/r/nsfw is here, the pertinent part of the HTTP transfer is below;
GET /r/nsfw HTTP/1.1
User-Agent: curl/7.34.0
Host: reddit.com
Accept: */*
HTTP/1.1 200 OK
Date: Mon, 29 Sep 10:28:51 GMT
X-Template: blacklisted
Content-Type: text/html
Content-Length: 195
Cache-Control: no-cache
X-Cache: MISS from Squid
Via: 1.1 Squid (squid/3.2.11)
Connection: keep-alive
< !DOCTYPE html>
Despite getting the correct A records back from the nameservers in packet 5 we can see in packets 12 onwards that the O2 Squid server (ironically the same software PacketFlagon.is uses to bypass censorship!) returns back some HTML with a meta refresh that instantly directs the browser to their block page.
As shown in this packet capture there is no IP/Host matching it is all done on the GET path and the Host header so Hosts files hacks won’t work either.
High Court blocks are solved using DNS and an attempt to resolve thepiratebay.se returns 127.0.0.1.
Finally some other blocks such as the block of torproject.org are achieved by just silently dropping the packets.
Starbucks – BT / Friendly WiFi
The people at Friendly WiFi appear to be quite zealous about blocking “pornography” and come out with ridiculous claims such as that by putting in their filtering one gets a “porn free city”
Thankfully their blocks are almost as easy to bypass as O2′s. Interestingly, unlike O2, Starbucks and BT don’t believe they are required to legally know who is using their WiFi and no registration is required.
DNS Spoofing: Yes
MiTM SSL: No
Deep Packet Inspection: Yes
Destination IP Transit Interference: No
Websites that are blocked due to sub-content (e.g. reddit.com/r/nsfw) are blocked over HTTP but accessible over SSL. Interestingly thepiratebay.se is reachable over SSL e.g.
curl -k -v https://194.71.107.27 -H 'Host: thepiratebay.se'
Using PAC files such as RoutingPacketsIsNotACrime.uk was hit and miss and requires some more investigation but other bypass options such as SSL, Tor and using an SSH SOCKS5 tunnel all worked without issue.
BT also force Google to downgrade search to a non-ssl version which means others could monitor your search terms.
Breaking down a BT Intercept
When trying to hit reddit.com/r/nsfw this packet capture shows a HTTP 302 is returned rather than the site we’re after.
GET /r/nsfw HTTP/1.1
User-Agent: curl/7.34.0
Accept: */*
Host: reddit.com
HTTP/1.1 302 Found
Location: http://217.41.225.106/redirect/starbucks/index.html
An attempt to reach thepiratebay.se resulted in a forged DNS reply for 193.113.9.167 that simply displays the words “Error – site blocked”
Interestingly as shown in this packet capture, resolving the A record out-of-band and then passing a HTTP request through works fine!
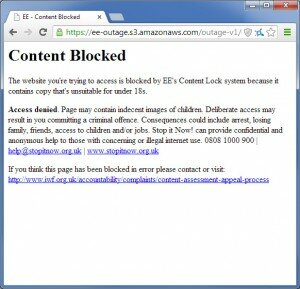
Bonus – EE Hotspot
During my travels between coffee shops I stumbled across an EE hotspot which had a completely different set of filtering as it uses OpenDNS.
DNS Spoofing: Yes
MiTM SSL: No
Deep Packet Inspection: No
Destination IP Transit Interference: No
Much like O2 you are required to register using a phone and EE uses www.picopoint.com to do this.
The filtering is very lax with reddit.com/r/nsfw and the Pirate Bay being allowed through however shock sites like rotten.com resolve to 67.215.65.130 which results in an OpenDNS block page.
Since the filtering is entirely DNS based out-of-band resolution, RoutingPacketsIsNotACrime, Tor and SSH SOCKS5 tunnels all work fine.
I’ve drank far too much coffee today and it’s a shame that public establishments feel it necessary to put censorship technology that performs excessive over-blocking (how is torproject.org sexual?) but at least it is still easy to bypass.