As mentioned on our Top Ways to Avoid Filters page the Onion Router Project (better known as TOR) excels at bypassing censorship technologies such as the Sky Broadband Shield, the TalkTalk filters, BT Parental Controls and even the Great Firewall of Cameron China whilst at the same time offering almost perfect anonymity.
TOR is an excellent choice for any would-be whistle blower, political journalist, privacy advocate, vulnerable adult or any other person who wants/needs unrestricted Internet access.
TOR is no more a tool for criminals than a kitchen knife or a car, much like encryption the more it is used by normal people for normal day-to-day tasks the better the protection for everyone by making it more expensive for nation states to perform blanket surveillance and Internet filtering.
This post will show you how to download and install the TOR client (which is easy) whilst also ensuring it’s the real deal and hasn’t been interfered with by your ISP or other malicious actors.
Downloading
The best place to download TOR is from the projects own website here: https://www.torproject.org/download/download-easy.html.en (note the https). You should also do whatever is necessary to acquire the signature file which can be found by following the link labelled sig (underlined in red below) on the download page.

The download is also available on this website by clicking here and the signature for this download is reproduced below.
-----BEGIN PGP SIGNATURE-----
Version: GnuPG v1
iQEcBAABCAAGBQJTaXIZAAoJEEFvBhBj/uZZEJsIAKD2Ny/oXZheHd3xkgk9t906
a3Xayel0Mxp7Yj6dEvoDKTvvkyvmN1PC4K7oFjovaFP29SekDSRvMYnRlLnDaEHD
QZoPs7bFpf1qoRukZgMr9Q9B4rsy4Q9hr8iNcV1OeVawiGf8aQ/9XIp3TDErb80w
0tKnK4JI0a8FDKumc5GFTNQNZo9G2r46puSu4hLkckbz8zZa4FqVIjOpiyG65ri4
VdujXmpObLYEL/lAfg6xoCIF8VzM9eb1jBj+ISCxt0r2bpD8/iBizEvNRjzWIQUe
krqEuPpzYNiGLzXvczMTULs4lo7s6jGDR44ztijnwm87JdJCtFIrrh/+8QKe82Q=
=h2XC
-----END PGP SIGNATURE-----
At this point you could just install TOR and trust that everything is OK but in this day and age you should really make sure.
Verifying the Download
At this point you should go off and read about GnuPG on Wikipedia and consider reading the GnuPG manual so you fully understand why we’re about to do what we are going to do.
As we’re on Windows (you should consider trying Linux even if it’s only on a live boot CD/USB) we need to install GPG4WIN which can be downloaded here: http://gpg4win.org/download.html. Pay close attention to the SHA1 checksum you will need that shortly.
Secondarily download and install the Microsoft File Checksum Integrity Verifier from, here: https://www.microsoft.com/en-gb/download/details.aspx?id=11533
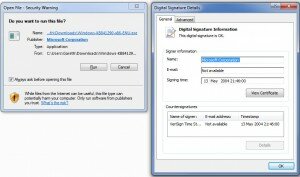
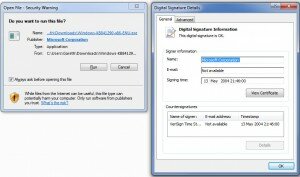
Luckily the Microsoft download will be signed and certified by a certificate already embedded in the OS so go ahead and install it, you should see that the publisher is “Microsoft Corporation” and if you click the blue text you should see a confirmation that the Digital Signature is OK;
Once extracted to a useful location (preferably the same place you downloaded the GPG4WIN installer to) execute the following command;
fciv.exe -sha1 gpg4win-2.2.1.exe
This will generate the SHA1 hash you noted earlier in a manner similar to that below, if the two hashes do not match exactly then something is wrong.
//
// File Checksum Integrity Verifier version 2.05.
//
6fe64e06950561f2183caace409f42be0a45abdf gpg4win-2.2.1.exe
Now (assuming that the hashes match) we need to install GPG4Win, for added security you can ensure that the certificate is also genuine for the installer by clicking More Details then Show information about this publishers certificate. The default GPG4Win installs options should suffice;

Once installed load up the GNU Privacy Assistant or GPA from the All Programs > Gpg4Win section of the start menu. GPA allows you to import the public keys of the TOR developers who signed the TOR installer to guarantee that it is genuine and hasn’t been tampered with.
All the signing keys can be found on this page; https://www.torproject.org/docs/signing-keys.html.en if you are unable to reach that page then the key we want is from a developer named Erinn Clark whose key can be identified as 0x63FEE659.
To install her key select Server then Retrieve Keys from the GPA menu

In the popup box that appears type or paste 0x63FEE659 then click OK.
 You should then be told that one 1 public key has been read and imported!
You should then be told that one 1 public key has been read and imported!

Select Erinn’s key from the list and look at the details, ensure that the fingerprint matches the one on https://www.torproject.org/docs/signing-keys.html.en or if you can’t reach that page this;
8738 A680 B84B 3031 A630 F2DB 416F 0610 63FE E659
If it does right click on her key and select Sign Key, this indicates that you trust this key for encryption and importantly for our purposes any signatures made.
You’re now ready to confirm if the TOR download is safe to install. Navigate to the location where you saved the TOR executable and the signature file, right click on the installer and navigate to More GpgEx Options then click Verify.

In the window that pops up click Decrypt / Verify, if all has been succesful you will see a green notice confirming that the signature passes.

You can now install TOR safe in the knowledge that the download has not been tampered with by malicious criminals or the surveillance state. Once installed you will now be able to evade any form of Government or ISP filtering.
Remember if you are using TOR to protect yourself as part of a whistle blowing exercise there are several warnings to take heed of to ensure that you do not jeopardise the work you’ve put in so far.